Cisa Known Exploited Vulnerabilities Catalog
Cisa Known Exploited Vulnerabilities Catalog - Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trump Apache shiro contains a vulnerability which may allow remote attackers to execute code or bypass intended access restrictions via an unspecified request parameter when a cipher key has not been configured for the remember me feature. Ingesting these known exploited vulnerabilities would be a valuable source for your siem/vm/xdr solution. Cisa adds osgeo geoserver geotools bug to its known exploited vulnerabilities catalog kaspersky leaves u.s. Cisa offers three different solutions to monitor the vulnerabilities: Monitor cisa known exploited vulnerabilities catalog. Cybersecurity and infrastructure security agency (cisa) added 185 vulnerabilities to its known exploited vulnerabilities (kev) catalog in 2024, as the database grew to 1,238 software and hardware flaws at high risk of cyberattacks. Cve appearing in the catalog will now contain a text reference and a hyperlink to the catalog. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. The nvd has added information to its cve detail pages to identify vulnerabilities appearing in cisa’s known exploited vulnerabilities (kev) catalog. Cisa offers three different solutions to monitor the vulnerabilities: The cybersecurity and infrastructure security agency (cisa) has recently updated its known exploited vulnerabilities (kev) catalog with four new vulnerabilities, adding to the growing list of cyber risks that have been actively exploited. Cybersecurity and infrastructure security agency (cisa) added 185 vulnerabilities to its known exploited vulnerabilities (kev) catalog in 2024, as the database grew to 1,238 software and hardware flaws at high risk of cyberattacks. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Cisa adds osgeo geoserver geotools bug to its known exploited vulnerabilities catalog kaspersky leaves u.s. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. Four have been exploited by known threat actors and employed in attacks. Monitor cisa known exploited vulnerabilities catalog. The nvd has added information to its cve detail pages to identify vulnerabilities appearing in cisa’s known exploited vulnerabilities (kev) catalog. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. Cisa adds osgeo geoserver geotools bug to its known exploited vulnerabilities catalog kaspersky leaves u.s. Apache shiro contains a vulnerability which may allow remote attackers to execute code or bypass intended access restrictions via an unspecified request parameter when a cipher key has not been configured. Cybersecurity and infrastructure security agency (cisa) added 185 vulnerabilities to its known exploited vulnerabilities (kev) catalog in 2024, as the database grew to 1,238 software and hardware flaws at high risk of cyberattacks. Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trump. Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trump For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. Four have been exploited by known threat actors and employed in attacks. Cisa adds osgeo geoserver geotools bug to its known exploited vulnerabilities catalog kaspersky leaves u.s. The cybersecurity and infrastructure security agency (cisa) has recently updated its known exploited vulnerabilities (kev) catalog with four new. Cisa offers three different solutions to monitor the vulnerabilities: For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. Monitor cisa known exploited vulnerabilities catalog. Market following the ban on the sale of its. Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trump Cve appearing in the catalog will now contain a text reference and a hyperlink to the catalog. Monitor cisa known exploited vulnerabilities catalog. It is recommended to dynamically ingest and alert new active. Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trump For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Monitor cisa known exploited vulnerabilities catalog. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. Cybersecurity and infrastructure security agency (cisa) added 185 vulnerabilities to its known exploited vulnerabilities (kev) catalog in 2024, as the database grew. The nvd has added information to its cve detail pages to identify vulnerabilities appearing in cisa’s known exploited vulnerabilities (kev) catalog. Cve appearing in the catalog will now contain a text reference and a hyperlink to the catalog. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. The cybersecurity and infrastructure security agency (cisa) has. In january 2025, fourteen vulnerabilities met the criteria for inclusion in the cisa’s kev catalog. Cve appearing in the catalog will now contain a text reference and a hyperlink to the catalog. The cybersecurity and infrastructure security agency (cisa) has recently updated its known exploited vulnerabilities (kev) catalog with four new vulnerabilities, adding to the growing list of cyber risks. Cisa adds osgeo geoserver geotools bug to its known exploited vulnerabilities catalog kaspersky leaves u.s. The nvd has added information to its cve detail pages to identify vulnerabilities appearing in cisa’s known exploited vulnerabilities (kev) catalog. Apache shiro contains a vulnerability which may allow remote attackers to execute code or bypass intended access restrictions via an unspecified request parameter when a cipher key has not been configured for the remember me feature. It is recommended to dynamically ingest and alert new active vulnerabilities in your environment. Cybersecurity and infrastructure security agency (cisa) added 185 vulnerabilities to its known exploited vulnerabilities (kev) catalog in 2024, as the database grew to 1,238 software and hardware flaws at high risk of cyberattacks. Cisa has added three new vulnerabilities to its known exploited vulnerabilities catalog, based on evidence of active exploitation. Ingesting these known exploited vulnerabilities would be a valuable source for your siem/vm/xdr solution. For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—cisa maintains the authoritative source of vulnerabilities that have been exploited in the wild. Four have been exploited by known threat actors and employed in attacks. Monitor cisa known exploited vulnerabilities catalog. Cve appearing in the catalog will now contain a text reference and a hyperlink to the catalog. Market following the ban on the sale of its software in the country fbi unlocked the phone of the suspect in the assassination attempt on donald trumpKnown Exploited Vulnerabilities (KEV) Catalog By CISA
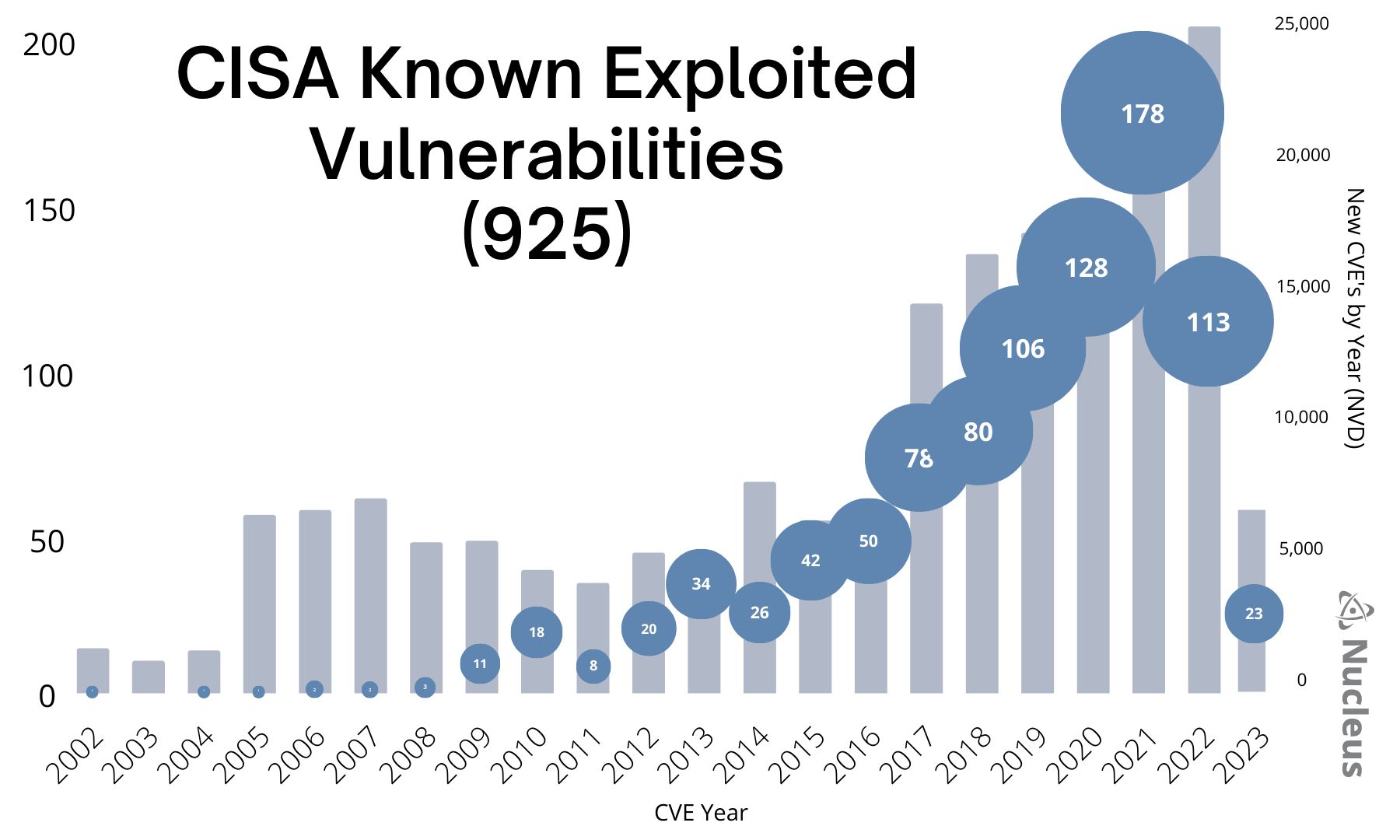
Analyzing 925 Known Exploited Vulnerabilities in the CISA KEV
CISA Adds New Known Exploited Vulnerabilities To Catalog
CISA KEV Blogs Stay tuned with latest updates and findings in cyber
Seven Known Exploited Vulnerabilities Added to CISA Catalog
CISA Adds Trimble Cityworks Vulnerability to Known Exploited
CISA Adds 6 Known Exploited Vulnerabilities to Catalog
CISA เพิ่มช่องโหว่ Apache Superset ลงใน Known Exploited Vulnerabilities
CISA Adds Actively Exploited Linux Kernel Vulnerability to Known
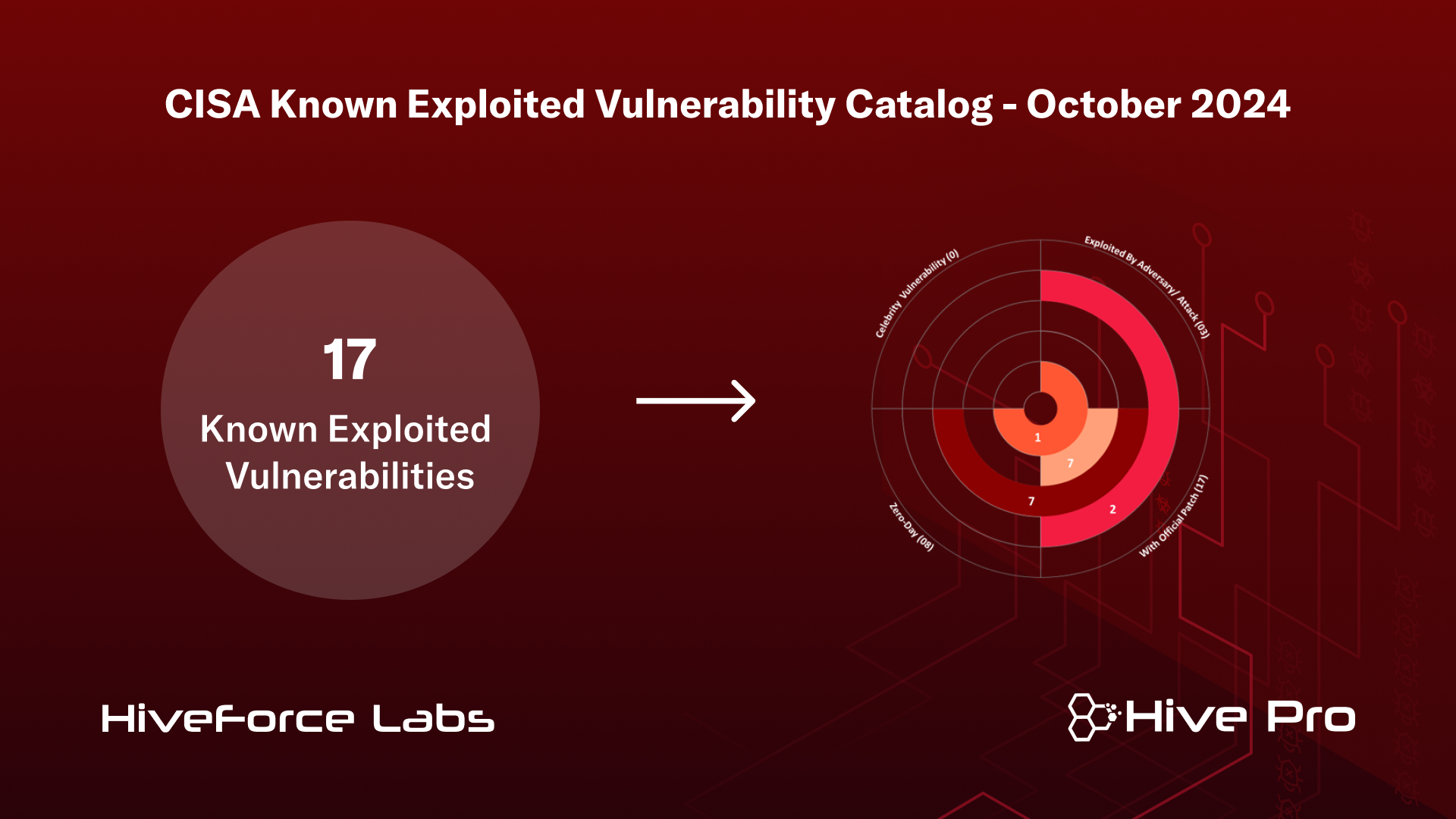
CISA's Known Exploited Vulnerability Catalog June 2024 HiveForce Labs
In January 2025, Fourteen Vulnerabilities Met The Criteria For Inclusion In The Cisa’s Kev Catalog.
Cisa Offers Three Different Solutions To Monitor The Vulnerabilities:
The Cybersecurity And Infrastructure Security Agency (Cisa) Has Recently Updated Its Known Exploited Vulnerabilities (Kev) Catalog With Four New Vulnerabilities, Adding To The Growing List Of Cyber Risks That Have Been Actively Exploited.
Related Post: